Will the U.S.-Iran Ceasefire Hold? – April 8 | Here's the Scoop
Source: Youtube

Will the U.S.-Iran Ceasefire Hold? – April 8 | Here's the Scoop
Source: Youtube
IBL News | New York
Cisco has launched DefenseClaw, a free, open-source security tool for OpenClaw that runs inside NVIDIA’s OpenShell this month.
In mid-March, at its GTC 2026 conference, NVIDIA announced NemoClaw and OpenShell to address security issues.
OpenShell provides the infrastructure-level sandbox that OpenClaw never had — kernel isolation, deny-by-default network access, YAML-based policy enforcement, and a privacy router that keeps sensitive data local.
It’s out-of-process enforcement, meaning the controls live outside the agent and can’t be overridden by it.
Cisco Systems is building on that foundation. Its AI Defense team published research showing how malicious skills exploit the trust model — through prompt injection, credential theft, and silent exfiltration — and released an open source Skill Scanner so the community could start vetting what they install.
OpenShell gives users a sandbox for the operational layer.
Sitting on top of OpenShell, Cisco introduced an open-source agentic governance layer, DefenseClaw, that scans everything before it runs. Every skill, every tool, every plugin, and every piece of code generated by the Claw gets scanned before it’s allowed into any Claw environment.
The scan engine includes five tools: skill-scanner, mcp-scanner, a2a-scanner, CodeGuard static analysis, and an AI bill of materials generator. Nothing bypasses the admission gate.
DefenseClaw detects threats at runtime — not just at the gate. Claws are self-evolving systems. A skill that was clean on Tuesday can start exfiltrating data on Thursday. DefenseClaw doesn’t assume what passed admission stays safe — a content scanner inspects every message flowing in and out of the agent at the execution loop itself.
Cisco explained:
“DefenseClaw enforces block and allow lists — and enforcement is not advisory. When you block a skill, its sandbox permissions are revoked, its files are quarantined, and the agent gets an error if it tries to invoke it. When you block an MCP server, the endpoint is removed from the sandbox network allow-list, and OpenShell denies all connections. This happens in under two seconds, no restart required. These aren’t suggestions. They’re walls.”
“And here’s the part that matters for anyone running Claws at scale: every claw is born observable.”
“DefenseClaw connects to Splunk out of the box. Every scan finding, every block/allow decision, every prompt-response pair, every tool call, every policy enforcement action, every alert — it all streams into Splunk as structured events the moment your claw comes online. You don’t bolt on observability after the fact and hope you covered everything. The telemetry is there from the beginning. The goal is simple: if your claw does something — anything — there’s a record.”
As an AI that reads personal files, manages tools, runs shell commands, and connects to platforms to build new capabilities, OpenClaw represents a paradigm shift — a new Jarvis — but it has also sparked one of the most concerning security crises in open-source history.
Within three weeks of it going viral, OpenClaw suffered a wave of serious security incidents that forced nation-states, restricted agencies, and companies to stop running it.
“I purposefully didn’t make OpenClaw simpler, but at the end of the day, if you build a hammer… You can hurt yourself. So should we not build hammers anymore?” explained the Austrian programmer who created OpenClaw.
Some vulnerabilities seen included:
• A critical remote code execution vulnerability; visiting a malicious webpage could hijack any agent.
• 135,000+ exposed OpenClaw instances on the public internet.
• A coordinated attack called ClawHavoc planted over 800 malicious skills in ClawHub — roughly 20 percent of the entire registry of productivity tools
• A security researcher created a malicious third-party skill that performed data exfiltration and prompted injection without user awareness, demonstrating security flaws in OpenClaw implementations.
To its credit, OpenClaw has been transparent about the risks, and the team has patched issues rapidly. But the structural reality is problematic: an agent with full system access, broad network reach, and a community-contributed skill ecosystem is a magnet for hackers.

Gilgo Beach serial killer Rex Heuermann pleads guilty to murdering 8 women
Source: Youtube

Israel claims 100 strikes in 10 minutes in Lebanon amid US-Iran ceasefire
Source: Youtube
IBL News | New York
Anthropic announced yesterday “Project Glasswing,“ a new initiative focused on global safety and security on the software side.
This new AI cybersecurity initiative has already garnered commitments from large technology companies, such as Apple, Amazon Web Services, Microsoft, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, the Linux Foundation, NVIDIA, and Palo Alto Networks
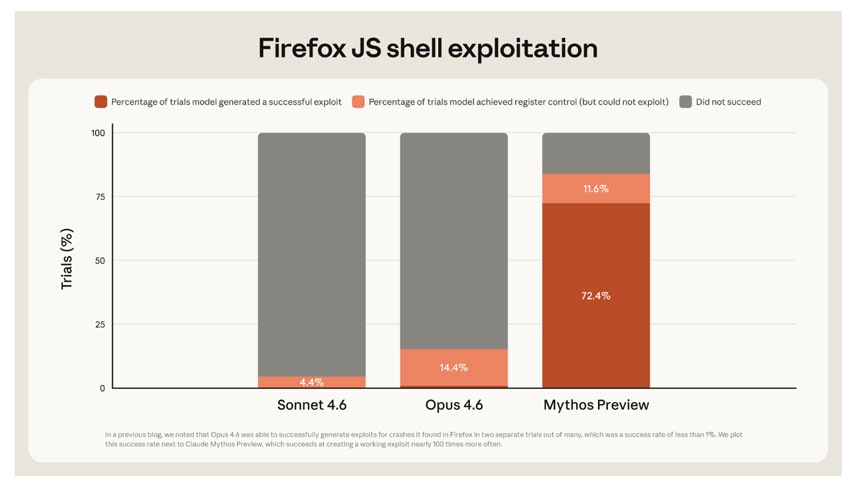
To enhance their security projects, participant companies that will have the chance to build on Project Glasswing will have access to Claude Mythos Preview, a new general-purpose language model for computer security tasks.
According to Anthropic, “Mythos Preview will help secure the world’s most critical software and prepare the industry for the practices we all will need to adopt to keep ahead of cyberattackers.”
The company said that Mythos Preview already found “thousands of high-severity vulnerabilities” in “every major operating system and web browser,” especially “in real open source codebases.”
Project Glasswing will help companies turn these capabilities “to work” and focus on “defensive purposes” against significant threats.
“Over 99% of the vulnerabilities we’ve found have not yet been patched, so it would be irresponsible for us to disclose details about them (per our coordinated vulnerability disclosure process). Yet even the 1% of bugs we are able to discuss give a clear picture of a substantial leap in what we believe to be the next generation of models’ cybersecurity capabilities—one that warrants substantial coordinated defensive action across the industry. We conclude our post with advice for cyber defenders today, and a call for the industry to begin taking urgent action in response.”
“During our testing, we found that Mythos Preview is capable of identifying and then exploiting zero-day vulnerabilities in every major operating system and every major web browser when directed by a user to do so. The vulnerabilities it finds are often subtle or difficult to detect. Many of them are ten or twenty years old, with the oldest we have found so far being a now-patched 27-year-old bug in OpenBSD—an operating system known primarily for its security.”
“Non-experts can also leverage Mythos Preview to find and exploit sophisticated vulnerabilities. Engineers at Anthropic with no formal security training have asked Mythos Preview to find remote code execution vulnerabilities overnight, and woken up the following morning to a complete, working exploit. In other cases, we’ve had researchers develop scaffolds that allow Mythos Preview to turn vulnerabilities into exploits without any human intervention.”
Glasswing is just the first step: patching and securing the world’s software infrastructure will be the work of months and years, and will require even broader cooperation across AI companies, cyberdefenders, software providers, governments, and more.
— Dario Amodei (@DarioAmodei) April 7, 2026

Intel Joins Musk’s Terafab Project With Tesla, SpaceX, xAI | Bloomberg Tech 4/7/2026
Source: Youtube

'Not a dry eye': NASA scientist recalls emotional Artemis II moment
Source: Youtube

NASA's Artemis II Successfully Slingshots Around the Moon
Source: Youtube

Iran crisis outlook: No clear path to deal as conflict risks rise
Source: Youtube

Breaking down Trump’s announcement of a two-week pause on Iran strikes
Source: Youtube